Blue Screen of Death: CrowdStrike's Global Outage and the Price of Trust
The Setup
What the world looked like at entry
CrowdStrike entered the summer of 2024 as cybersecurity's undisputed heavyweight. The stock had surged from $282.64 in mid-April to nearly $390 by early July, riding a wave of enterprise security spending and AI-powered threat detection hype. At its peak, CrowdStrike commanded a premium valuation that reflected the market's belief in both the company's technological moat and its mission-critical role in protecting global IT infrastructure. Then, on July 19, a single faulty configuration update turned that trust into the largest IT outage in history.
The Falcon sensor update—Channel File 291—bricked approximately 8.5 million Windows machines worldwide. Airlines grounded flights. Hospitals lost access to patient records. Banks froze. The Blue Screen of Death became a global news event, and CrowdStrike's stock cratered from $383.57 to a low of $200.81 in just three weeks—a 47.6% peak-to-trough collapse. The company that sold protection against catastrophic IT failures had become one. Delta Air Lines alone canceled over 5,000 flights and would later sue for $500 million in damages.
This case study follows a 14-week holding period from entry at $304.96 through exit at $300.62—a -1.42% loss that underperformed the S&P 500 by 6.89 percentage points. But the headline return masks the real story. The position endured a 28.6% drawdown to a closing low of $217.89 before an improbable recovery brought the stock nearly back to breakeven. It is a case study in operational risk, the stickiness of mission-critical software, and the market's willingness to forgive a monopoly-adjacent franchise even after a catastrophic self-inflicted wound.
MACRO REGIME
- Fed Funds rate at 5.25–5.50%, with markets debating the timing of the first cut
- AI infrastructure spending accelerating across enterprise technology
- Cybersecurity budgets elevated due to rising nation-state and ransomware threats
- Tech sector broadly strong, with the S&P 500 near all-time highs
- Geopolitical tensions (Russia-Ukraine, Middle East) underscoring the need for cyber defense
COMPANY SETUP
- CrowdStrike had grown annual recurring revenue (ARR) past $3.5 billion, with 33%+ year-over-year growth
- The Falcon platform had expanded from endpoint detection to a full cybersecurity suite (cloud, identity, SIEM)
- Stock had rallied from $282.64 (week of April 15) to $389.68 (week of July 1)—a 38% run in under three months
- Valuation stretched: trading at 75x+ forward earnings and 25x+ forward revenue
- Management touting "platformization" strategy to consolidate customer security spending
- Module adoption rates increasing—customers using 5+ modules trending upward
SECTOR MOMENTUM
- Palo Alto Networks had pivoted to a platformization strategy, briefly pressuring its own stock in February 2024
- SentinelOne positioned as the primary alternative in endpoint detection
- Microsoft expanding its own security suite, creating long-term competitive concern
- Enterprise security spending seen as non-discretionary, insulating the sector from macro weakness
- Multiple high-profile breaches (Change Healthcare, AT&T) reinforcing urgency of cyber defense
SENTIMENT
- Overwhelmingly bullish: 40+ analysts covering with median price target above $350
- CrowdStrike seen as the "must-own" name in cybersecurity
- Stock had pulled back from $385.44 (week of June 10) to $371.32 (week of July 8)—a modest dip
- No material concerns flagged about update deployment practices or operational risk
- Retail and institutional investors both heavily positioned
Entry Point
The thesis and the position

A trader entering CrowdStrike in mid-July might have seen an attractive pullback opportunity. The stock had retreated roughly 5% from its June highs, offering a rare entry point into a company growing revenue at 30%+ with best-in-class retention metrics. The cybersecurity spending cycle showed no signs of slowing, and CrowdStrike's platform strategy was gaining traction with large enterprises consolidating vendors. The pullback to $371.32 in the week of July 8 looked like a normal breather after a powerful three-month run.
The risk that materialized was not one that any analyst was modeling. CrowdStrike's Falcon sensor operated at the kernel level of Windows operating systems—the deepest possible access point. This architecture was the source of both its competitive advantage (superior threat detection) and its catastrophic vulnerability (a bad update could brick entire fleets of machines). The company pushed content updates to millions of endpoints automatically, without staged rollouts or customer-controlled deployment windows. This operational practice was hiding in plain sight, but virtually nobody was pricing the tail risk of a faulty update distributed simultaneously to 8.5 million machines. The market was paying a premium for CrowdStrike's scale and ubiquity without discounting the systemic risk that came with it.
Before continuing: Consider what you would have done.
The Journey
From entry to exit
Key Events
| Date | Event | Category | Stock Reaction |
|---|---|---|---|
| Jul 15, 2024 | Entry week opens at $371.67 | Entry | Starting point |
| Jul 19, 2024 | Falcon sensor Channel File 291 update brakes 8.5M Windows machines globally | Operational | Stock crashes to $290.10 intraweek, closes at $304.96 |
| Jul 19, 2024 | Airlines ground flights; hospitals, banks, emergency services disrupted worldwide | Operational | Included in crash week |
| Jul 22-26, 2024 | Remediation continues; most systems require manual intervention (boot to Safe Mode, delete file) | Operational | Stock falls to $256.16 weekly close |
| Jul 24, 2024 | Microsoft reports 8.5 million Windows devices affected | Operational | Selling intensifies |
| Jul 29, 2024 | CrowdStrike reports 99% of sensors back online; stock hits trade-period closing low of $217.89 | Operational/Recovery | Maximum drawdown week—$217.89 close |
| Aug 5, 2024 | Stock hits absolute low of $200.81 intraweek before recovering to close at $240.90 | Technical | Capitulation and reversal |
| Aug 6, 2024 | CrowdStrike publishes 12-page Root Cause Analysis report | Operational | Begins rebuilding credibility |
| Aug 28, 2024 | Q2 FY2025 earnings: revenue $964M (+32% YoY), 97% gross retention rate | Earnings | Stock stabilizes in $270s |
| Sep 2, 2024 | Broader market selloff; CRWD pulls back to $246.39 close | Macro | Correlated decline |
| Sep 16, 2024 | Recovery accelerates; stock closes at $299.85—first close near $300 since the crash | Recovery | Approaching entry price |
| Oct 7, 2024 | Stock hits $322.59 intraweek high; analyst upgrades cite minimal customer churn | Recovery | Brief move above entry |
| Oct 21, 2024 | Exit week at $300.62; Delta lawsuit headlines add late headwind | Legal/Exit | Trade ends near breakeven |
| Oct 25, 2024 | Delta files $500M lawsuit; CrowdStrike countersues | Legal | Post-exit event |
How It Unfolded
Phase 1: The Crash (July 15-29) The outage on July 19 was a Black Swan for CrowdStrike shareholders. The stock opened the week at $371.67 and closed at $304.96—but that was just the beginning. The following week brought relentless selling as the full scope of the disaster became clear. Airlines had grounded thousands of flights. Hospitals had lost systems. Fortune 500 companies estimated combined losses exceeding $5.4 billion. The healthcare sector alone absorbed an estimated $1.94 billion in damages.
CrowdStrike's stock fell to $256.16 by July 22 and then to $217.89 by July 29—the worst weekly close of the entire trade. From the pre-crash intraweek high of $383.57, the stock had lost 43.2% in just two weeks. Each day brought new headlines about affected organizations, manual remediation requirements (boot to Safe Mode, navigate to the CrowdStrike directory, delete the offending .sys file), and questions about whether CrowdStrike's enterprise customers would defect.
Phase 2: Capitulation and Stabilization (August 5-26) The first week of August brought the absolute low: $200.81 intraday on August 5, representing a 47.6% decline from the pre-crash high. But the week also brought the first real sign of stabilization. The stock recovered to close at $240.90—a $40 intraweek reversal that suggested sellers were exhausting themselves.
On August 6, CrowdStrike published its formal Root Cause Analysis, identifying the mismatch between 21 expected input fields and 20 provided fields in the content interpreter as the technical cause. The transparency helped. By mid-August, the stock had climbed back to $262.54, and the August 28 Q2 earnings report delivered surprisingly strong numbers: $964 million in revenue (up 32% year-over-year) and a 97% gross retention rate. CrowdStrike disclosed approximately $60 million in expected revenue impact from "customer commitment packages"—essentially discounts offered to retain affected clients—but the market was relieved it was not worse. The stock closed at $271.54 for the week of August 19 and $277.28 for August 26.
Phase 3: The Macro Headwind (September 2-9) Just as CrowdStrike was stabilizing, the broader market pulled back. The S&P 500 declined from $563.68 to $540.36 in the week of September 2, and CrowdStrike fell in sympathy to $246.39—its second-lowest close of the trade period. This was a frustrating setback for bulls who had watched the recovery unfold through August, but it was clearly macro-driven rather than company-specific.
Phase 4: The Recovery Rally (September 16 - October 14) This is where the trade got interesting. Starting in mid-September, CrowdStrike mounted a powerful recovery. The stock surged from $259.13 to $299.85 in the week of September 16—a 15.7% weekly gain—as multiple analysts upgraded their outlooks citing minimal customer churn. SentinelOne and Palo Alto Networks had reported fielding inquiries from CrowdStrike customers, but the actual defection rate appeared minimal. CrowdStrike's platform was too deeply embedded in enterprise security stacks to rip out easily.
By the week of October 7, the stock hit $322.59 intraweek—briefly trading above the entry price and 60% above the August low. Morgan Stanley raised its price target to $390, and KeyBanc lifted its target to $480, both maintaining overweight ratings. The recovery narrative was taking hold: CrowdStrike had survived the worst IT outage in history with its customer base largely intact.
Phase 5: Late Headwinds and Exit (October 14-21) The final two weeks brought a pullback from the recovery highs. Delta Air Lines' impending lawsuit weighed on sentiment, and the stock retreated from $320.21 to $310.15 and then to $300.62—the exit price. The recovery had stalled just below breakeven, leaving the trade with a -1.42% loss after three months of extreme volatility.
Exit
- Date: October 21, 2024
- Price: $300.62
- Context: The exit came as the initial recovery rally was fading. CrowdStrike had proven its customer base was sticky—97% gross retention and minimal churn—but the stock still carried the overhang of ongoing litigation, including Delta's forthcoming $500 million lawsuit filed on October 25. The recovery from $200.81 to $300.62 was remarkable, but it left shareholders who entered at $304.96 with a small loss and significant psychological scarring from the 28.6% drawdown.
Price Action
The trade in chart form
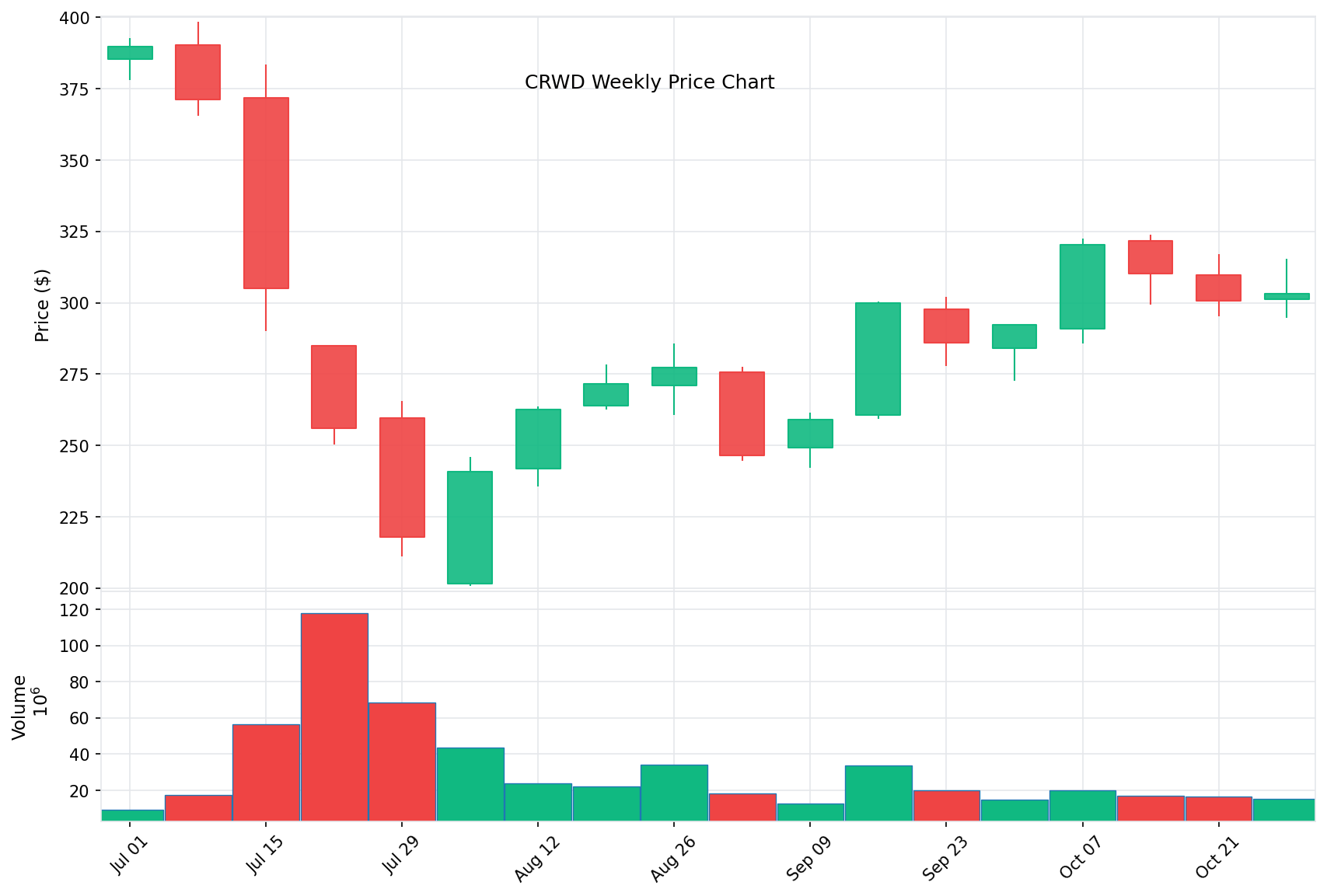
Weekly closing prices showing the crash from $304.96 to $217.89, the capitulation low of $200.81, and the recovery rally back to $300.62. The V-shaped pattern reflects the market's rapid reassessment from panic to recognition that CrowdStrike's franchise remained intact.
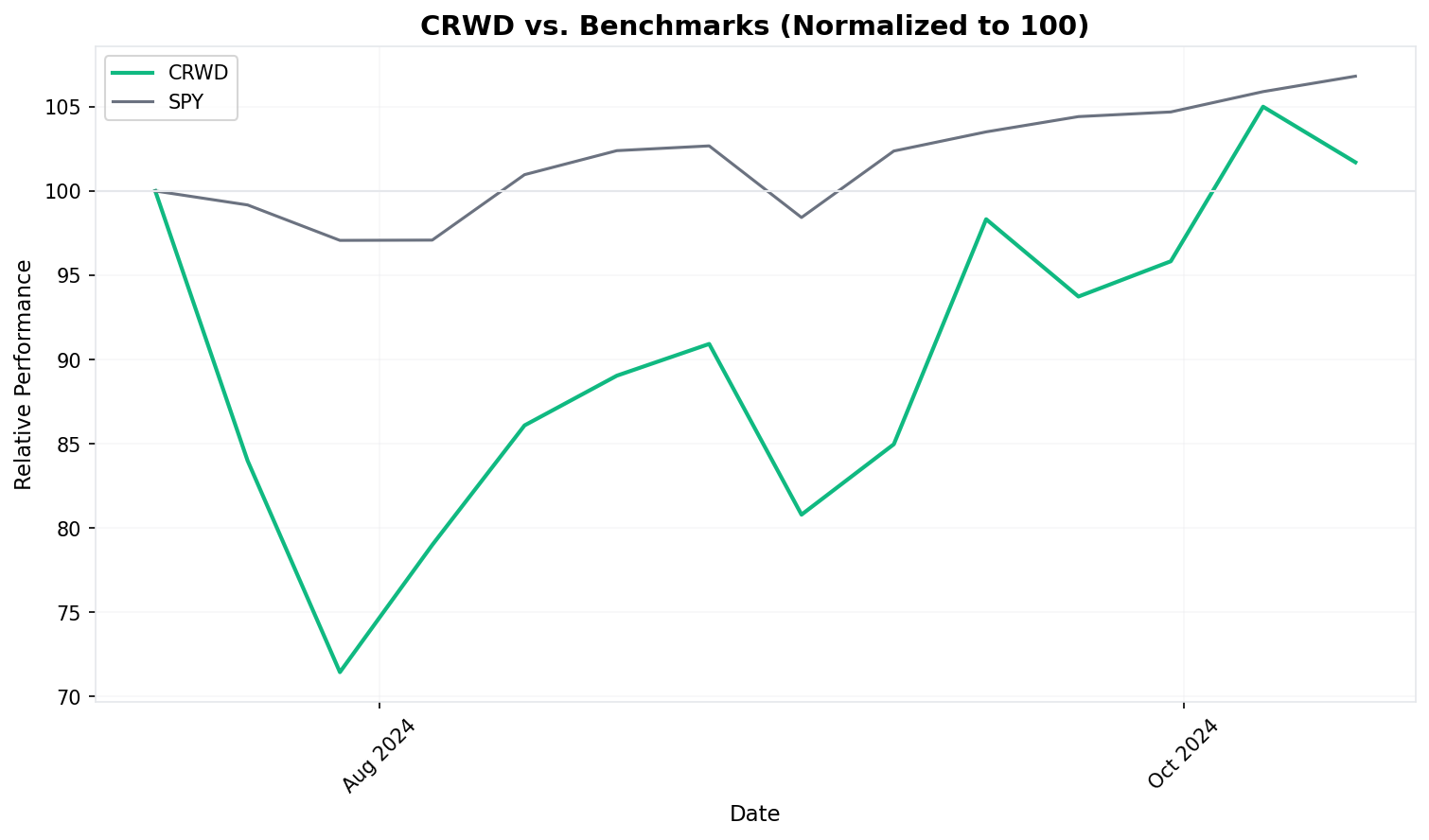
CrowdStrike vs. S&P 500 relative performance, rebased to 100 at entry. While SPY steadily climbed to 105.5 by exit, CRWD plunged to 71.4 at its closing low before recovering to 98.6. The divergence peaked in late July and early August before narrowing through September and October.
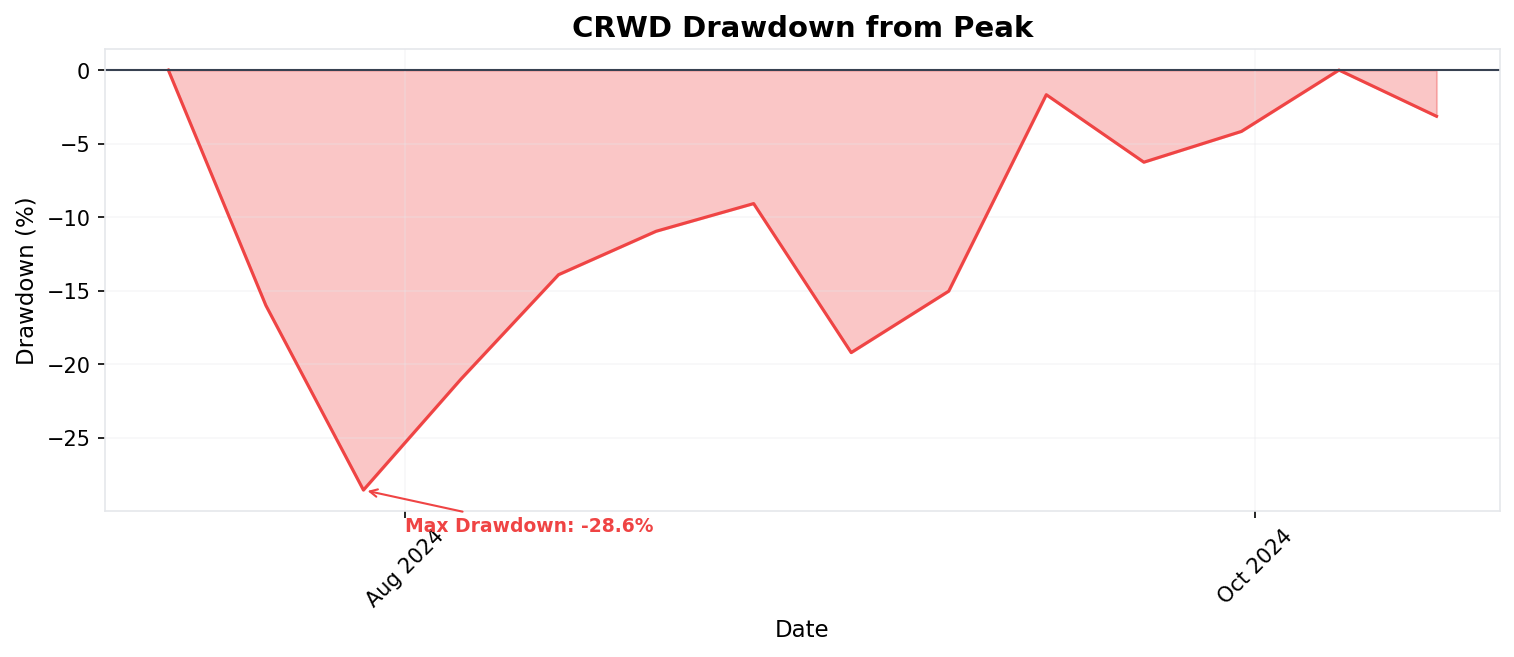
Drawdown chart showing the depth and duration of the decline. The position spent 10 of 15 weeks underwater by more than 10%, with the maximum drawdown of 28.6% (close basis) occurring just two weeks after entry. The rapid recovery was impressive but insufficient to generate a positive return.
Results
The final accounting
CrowdStrike underperformed the S&P 500 by 6.89 percentage points over the 14-week period. While the headline loss was modest, the path was brutal—the position experienced a 28.6% drawdown while the S&P 500 never declined more than 5.2% from its starting point. On a risk-adjusted basis, this trade was significantly worse than the raw return suggests.
Lessons
What the trade revealed
What Worked
-
Customer retention proved the moat. The single most important data point in this entire case study was CrowdStrike's 97% gross retention rate reported at Q2 earnings. Despite the worst operational failure in IT history, almost no customers actually left. CrowdStrike's Falcon platform was too deeply integrated into enterprise security operations—ripping it out and replacing it with SentinelOne or Palo Alto Networks would take months and introduce its own risks. This stickiness is what made the recovery possible.
-
Transparent crisis response limited the damage. CrowdStrike published a detailed Root Cause Analysis on August 6—less than three weeks after the outage—that was technically specific and accepted full responsibility. CEO George Kurtz appeared on national media immediately. The company did not deflect blame or minimize the impact. In an era of corporate spin, the straightforward mea culpa preserved institutional credibility with enterprise buyers who needed a reason to stay.
-
The outage was a content update, not an architecture failure. The root cause was a mismatch between template fields in a configuration file—essentially a quality assurance failure in the update pipeline. It was not a fundamental flaw in CrowdStrike's detection engine or platform architecture. This distinction mattered enormously. The fix was procedural (add bounds checking, implement staged rollouts) rather than architectural, which meant the recovery could be fast and credible.
-
Strong Q2 earnings reframed the narrative. Revenue of $964 million growing 32% year-over-year reminded the market that CrowdStrike's underlying business was never broken. The $60 million revenue impact from customer commitment packages was a rounding error on a $3.86 billion ARR base. Earnings transformed the conversation from "will CrowdStrike survive?" to "how fast will CrowdStrike recover?"—a dramatically different question.
What Didn't Work
-
The entry captured the crash but not the recovery. Entering at $304.96 meant buying after the initial Friday selloff but before the real damage was done over the following two weeks. A trader who waited until the capitulation low near $200.81 in early August would have captured a 50%+ return by October. The entry timing was the worst possible combination: late enough to miss the pre-crash price, early enough to absorb the full drawdown.
-
Operational risk was completely unpriced. Before July 19, no analyst model included a scenario where CrowdStrike's own update process could brick millions of client machines. The stock's premium valuation reflected growth and competitive positioning but zero discount for the tail risk of a company that pushes kernel-level updates to 8.5 million machines without staged rollouts. The market learned this lesson the hard way.
-
Competitor threats proved hollow but created uncertainty. SentinelOne CEO Tomer Weingarten publicly stated the outage's effects would "play out for years" and reported fielding new customer inquiries. Palo Alto Networks similarly reported conversations with CrowdStrike customers exploring diversification. While the actual defection rate was minimal, these headlines created overhang during the recovery and contributed to the stock's inability to reclaim its pre-crash levels within the trade period.
-
Litigation risk capped the recovery. Delta's $500 million lawsuit—filed four days after the trade exit—was telegraphed for weeks and weighed on sentiment throughout October. CrowdStrike's contracts generally cap liability at the value of the subscription (roughly $10 million in Delta's case), but the headline risk and legal uncertainty made institutional buyers hesitant to aggressively bid the stock back to pre-crash levels.
Key Takeaways
-
Mission-critical software has asymmetric risk profiles. CrowdStrike's value proposition—deep, kernel-level access to protect endpoints—was also its greatest vulnerability. When the same architecture that provides superior protection can also cause catastrophic failure, valuation models need to incorporate tail risk, not just growth rates. Investors in companies with privileged system access should always ask: "What happens if a bad update goes out to every customer simultaneously?"
-
Switching costs are the ultimate moat in a crisis. The 97% retention rate was not about forgiveness—it was about friction. Replacing an endpoint detection platform across tens of thousands of machines, retraining security operations teams, and re-integrating with existing security stacks is a multi-month, multi-million-dollar project. CrowdStrike survived not because customers were happy, but because leaving was harder than staying. For investors, this is a reminder that high switching costs protect equity value even in worst-case scenarios.
-
Crisis management matters as much as crisis prevention. CrowdStrike's response—immediate public acknowledgment, rapid technical remediation (78-minute time to revert), transparent Root Cause Analysis within three weeks, and customer commitment packages—was textbook crisis management. Contrast this with companies that minimize, deflect, or delay disclosure. The speed and transparency of the response was a material factor in the stock's recovery and should be weighted in any post-crisis investment analysis.
-
Drawdown magnitude matters more than endpoint return. This trade ended at -1.42%—nearly breakeven. But the 28.6% drawdown (34.2% intraweek) would have tested any position-sizing framework. A portfolio with a 5% allocation to CRWD would have experienced a 1.4% portfolio-level drawdown, while a concentrated 20% position would have suffered a 5.7% hit. The lesson is not about whether the stock recovered, but whether you could have held through the worst of it. Most traders cannot, and those who sold near the lows locked in devastating losses.
-
Post-crisis recovery trades require patience and conviction. The most profitable trade in this entire episode was not the entry at $304.96 but rather buying during the capitulation low in early August near $200-$218. Identifying that CrowdStrike's franchise was intact despite the operational failure, and having the conviction to buy when headlines were worst, would have generated 40-50% returns in two months. The broader lesson: the best returns in crisis situations come not from holding through the crash, but from deploying fresh capital when the market is pricing permanent impairment and the fundamentals suggest temporary disruption.
Sources
- CrowdStrike: Technical Details on Falcon Update for Windows Hosts — CrowdStrike's official technical blog post on the outage.
- Channel File 291 Incident: Root Cause Analysis — CrowdStrike's formal RCA published August 6, 2024.
- 2024 CrowdStrike-related IT outages — Wikipedia — Comprehensive timeline of the global impact.
- CrowdStrike outage explained: What caused it and what's next — TechTarget — Technical breakdown and industry analysis.
- Widespread IT Outage Due to CrowdStrike Update — CISA — U.S. government cybersecurity agency alert.
- CrowdStrike Reports Q2 FY2025 Financial Results — Official earnings release showing 97% retention and $964M revenue.
- CrowdStrike Q2 earnings report — CNBC — Analysis of Q2 results and outage impact.
- Delta, CrowdStrike sue each other over widespread IT outage — CNBC — Coverage of the $500M dueling lawsuits.
- Delta sues CrowdStrike over software update — CNN Business — Details on Delta's 5,000+ canceled flights and $500M damages claim.
- SentinelOne fields inquiries from new customers following CrowdStrike outage — Cybersecurity Dive — Competitor response and market dynamics.
- CrowdStrike's rivals stand to benefit from its update fail debacle — TechCrunch — Immediate competitor analysis post-outage.
- CrowdStrike takes a revenue hit as global IT outage reckoning lingers — Cybersecurity Dive — Ongoing financial impact assessment.